Committee Stage Insights on the Cyber Security and Resilience Bill
17 February 2026

The committee stage hearings on the Cyber Security and Resilience Bill have brought together voices across from the industry, including regulators, public bodies and academia, to scrutinise the government’s flagship cyber resilience legislation and expand on the existing framework of the Network and Information Systems (NIS) regulations.
Although there seems to be a general consensus that the Cyber Security and Resilience Bill acts as a positive step to strengthen resilience in some of the UK’s more vulnerable sectors, the committee stage hearings saw a number of critiques raised against the current version of the Bill.
There was notable tension between the Government’s push for regulatory agility against systemic threats and industry demands for definitional clarity and legal certainty. The Bill dramatically expands the NIS regulatory perimeter to encompass data centres, large load controllers, and Managed Service Providers (MSPs), introducing powers to designate critical suppliers based on a cumulative five-step test.
One central issue lies in the government’s reliance on secondary legislation to define key thresholds, argued as necessary to keep pace with threats like AI, but which critics fear creates a disproportionate, costly, and legally ambiguous compliance burden, especially for small and medium-sized enterprises (SMEs).
Other key takeaways from the committee stage include:
- Scope, Outcomes, and Thresholds: Kanishka Narayan MP, Minister for AI, defended the Bill’s ‘outcomes’ focus for addressing frontier risks (AI/quantum) and pre-positioning threats. However, RUSI argued the scope should shift from sectoral lists to ‘impact-based’ thresholds, such as FTSE350 companies, suggesting the public/private divide is the wrong metric.
- Uncertainty and SME Burden: The ICO stressed the need for precise secondary legislation and clear definitions to issue generic advice. Parliamentarians, including Ben Spencer MP, warned that leaving too much detail to future regulations creates legal jeopardy and a disproportionate compliance burden on SMEs, risking a ‘chilling effect’ on the UK tech sector.
- Critical Supplier Designation Test and Vagueness: Kanishka Narayan MP clarified the designation mechanism as a cumulative five-step test intended as a safeguard. Yet, Ben Spencer argued the definition remains so vague that non-critical services could technically be designated, while Palo Alto Networks (PAN) argued the regime should be limited to suppliers with systemic importance across multiple sectors.
- Reporting Logistical and Legal Barriers: Regulators (ICO, Ofcom) and Parliamentarians (Alison Griffiths) strongly argued for a single, consolidated incident reporting portal to prevent firms from having to report the same event to multiple bodies (GDPR, NIS, etc.). Professor John Child also highlighted the Computer Misuse Act (CMA) as a barrier, as it criminalises legitimate security testing, discouraging professionals from documentation and reporting.
- Governance, Culture, and Regulatory Cost: Industry voices (Fortinet, PAN, Worshipful Company of Information Technologists) unanimously argued that cyber must be treated as a board-level business risk. Conversely, Parliamentarians (Ben Spencer) criticised the Minister’s defence of the new power allowing regulators to charge fees, arguing it could act as an ‘operational tax’ that diverts funds away from actual security improvements.
The Bill Committee will now digest the evidence presented to them and produce a report scheduled to be published on 3rd March, that will outline recommendations and amendments for the Bill prior to its third reading in the House of Commons.
If you have any questions about the Cyber Security and Resilience Bill, committee stage scrutiny, or how this new legislation may affect your business, please get in touch at secretariat@cb-network.org.
Cyber Security and Resilience Bill second reading and Cyber Action Plan announcement – What do Westminster’s latest moves mean for the UK cyber sector?
8 January 2026

On 6 January 2025, Westminster sent a clear signal that the UK’s cyber agenda is shifting from strategy and planning to practical implementation. On the same day that the Cyber Security and Resilience Bill cleared its second reading in the House of Commons, the government also unveiled its Cyber Action Plan, backed by £210 million to strengthen cyber defences and digital resilience across government departments and the wider public sector.
Taken together, these moves signal momentum from the government toward tightening the UK’s cyber regulatory framework and raising the baseline for cyber resilience across the economy. However, many may be unsure of what these mean for affected industries and sectors.
This article will explore what the Cyber Security and Resilience Bill’s second reading and the new Cyber Action Plan mean in practice – for the areas and organisations directly in their scope, for those in their ecosystems, and for the cyber industry more broadly that will be tasked with supporting businesses through the transition.
Cyber Action Plan
On the 6th January, as many in the sector awaiting the scheduled second reading of the Cyber Security and Resilience Bill, the government made a surprise announcement of its Cyber Action Plan, which set out plans to strengthen cyber defences and digital resilience across government departments and the public sector, backed by £210m of government funding.
The plan focuses on three key outcomes: clearer visibility of cyber risks, faster incident response, and stronger collective action so that no single organisation is left to manage the aftermath of an attack on their own. At its heart is a proposed ‘Government Cyber Unit’, which is expected to coordinate efforts and operations to implement the plan and measure its success.
Crucially, the Cyber Action Plan is designed to underpin the government’s broader digital transformation agenda within the public sector and government departments. This includes further digitisation of public services, improving the accessibility of online services, reducing virtual queues, and providing more centralised access to government resources and support. Through this, the government hopes to unlock up to £45bn in productivity savings across the public sector through this plan, hence the interest in improving cybersecurity and operational resilience.
The plan also introduces the new ‘Software Security Ambassador Scheme’, aiming to tackle software supply chain risk through a new, voluntary ‘Software Security Code of Practice’. This is effectively a best‑practice checklist for secure software development, with public sector suppliers expected to demonstrate alignment with these practices. Early ambassadors include Cisco, Palo Alto Networks, Sage, Santander and NCC Group.
Through the plan, government departments are expected to be held to standards equivalent to those set out in the Cyber Security and Resilience Bill. For those providing cyber security services to the public sector, this could signal an increase for risk assessment, incident response and monitoring solutions as departments look to meet milestones in the plan and modernise their systems securely.
Cyber Security and Resilience Bill second reading
Following the Cyber Action Plan announcement, the government’s Cyber Security and Resilience Bill cleared its second reading in the House of Commons, receiving a broadly positive reception in the House. This was largely expected for a measure aimed at updating and extending the UK’s cyber regulatory framework for a more connected and tech‑dependent economy.
Introducing the Bill, DSIT Minister of State Ian Murray made the case that cyber resilience is not only a security necessity, but also an economic growth issue. MPs focused their scrutiny on three questions: whether the Bill’s scope matches the risk landscape, whether it could create a disproportionate burden on businesses, and whether regulators will be equipped to enforce the new regime effectively.
Substantively, the Bill builds on the 2018 NIS regulations by bringing large load controllers, data centres and managed service providers into scope, and aims to ‘future-proof’ the legislation by including mechanisms to adapt the perimeter over time as technology and risks evolve.
A constructive debate, with three core concerns
A range of MPs took part in the debate, including Shadow teams and backbenchers. While the overall tone was constructive and MPs broadly welcomed the extension of regulations, much of the regulatory scrutiny centred around three areas:
1) Scope: does the Bill match the risk landscape?
One concern was whether the Bill truly takes a ‘whole‑of‑economy’ approach. MPs questioned if its scope covers the businesses and services most at risk and most economically damaging if hit by a cyberattack. They highlighted major private sector firms recently targeted by cyber incidents, such as Jaguar Land Rover, M&S and the Co‑op, that fall outside its remit.
While not classed as critical national infrastructure, disruption to these companies could trigger widespread supply chain issues, consumer impact, and broader economic damages. MPs also pointed to sectoral gaps, notably in financial services, which could fragment the national approach as different regimes run in parallel.
Finally, they scrutinised new ministerial powers offered to the DSIT Secretary of State to reclassify sectors as critical infrastructure, raising concerns around accountability and transparency.
2) Burden on business: necessary regulation or risking overreach?
The second major theme was the Bill’s burden on businesses, and whether the compliance model is proportionate.
A core concern was potential duplication. MPs noted that the Bill’s incident‑reporting and compliance duties may overlap with existing regulatory regimes, particularly the UK GDPR. For organisations already navigating multiple reporting and governance frameworks, the risk is that new obligations complicate pre-existing compliance without necessarily improving security outcomes.
MPs also raised the question of proportionality across company size. While the costs and operational changes implied by the Bill may be manageable for larger firms, there was concern that they could function as a de facto “operational tax” on SMEs. Opposition MPs viewed this as punitive, while carrying the perception that the bill did not go far enough to enforce board-level accountability.
3) Regulators: are they capable of enforcement?
The third set of concerns related to regulators, both in their ability to deliver the new regime and the risk of unintended consequences.
Firstly, MPs questioned whether regulators will have the resources and expertise needed to enforce the new responsibilities consistently. A particular issue raised was timing: additional funding is expected to arrive only after the Bill, leaving little support during the transition period before the Bill is implemented. Some fear that this gap could create uneven implementation, slow readiness, and inconsistent enforcement across sectors.
Secondly, MPs raised concerns about the funding regime for regulators. If regulators become reliant on fee income, MPs warned this could create perceived or real incentives to expand scope or increase supervisory activity in ways that may feel unfair or disproportionate.
Additional points to note
Furthermore, MPs stressed the point that legislation is only one part of improving national cyber defences. They stressed that the government needs to continue to hold industry to account through governance, encouraging them to take up effective cyber insurance by industry, promote cyber education, and improve skills, addressing the reality that individuals are often the weakest link.
In addition to these three key areas, there were also concerns around whether the legislation would keep pace with fast‑moving threats (AI‑enabled attacks, credential misuse) when many breaches now involve the use of compromised, but valid, credentials. In this way, there were questions around whether legislation would be enough to tackle what may be seen as effective governance/business culture failures.
Finally, there were concerns raised around data sovereignty, with many businesses reliant on the reliance on US hyper-scalers and calling for the consideration of supplier concentration and dependency as a strategic priority.
Next steps: Public Bill Committee on 3 February
The Bill now moves into the Public Bill Committee stage, where MPs will scrutinise it in more detail. The first session is scheduled for 3rd February 2025. Within this stage, there will be a call for evidence which will allow industry voices to contribute to this debate and shape the legislation going forward. CBN is considering submitting evidence to the committee
If you’d be interested in hearing more about what’s to come with the Cyber Security and Resilience Bill, CBN will be discussing the Bill at our January Members Meeting in London, on Wednesday, 21st January, 4:30pm – 7:30pm. Alongside our deep dive into the Bill, this event will also consist of a roundtable style discussion to help shape our priorities for 2026.
If you’d like to join us for our members meeting, please head to cb-network.org/join-us/.
Otherwise, feel free to drop us a message at secretariat@cb-network.org.
APPG for Cyber Innovation publishes feedback on the CSR Bill

The Cyber Innovation APPG publishes feedback on the upcoming Cyber Security & Resilience Bill. In this document, the All-Party Group provides an initial view on the upcoming Cyber Security and Resilience (CSR) Bill. It has been informed through a survey with 89 respondents from across the cyber sector and beyond, as well as input from a parliamentary roundtable discussion held under the Chatham House rule that brought together 17 representatives from Managed Service Providers (MSPs), cyber companies, academics and other organisations.
This document is aimed at supporting the development of the CSR Bill, and the Cyber Innovation APPG would be happy to facilitate further engagement between the Department for Science, Innovation and Technology (DSIT), Parliament, and the wider sector. The Bill provides a unique opportunity to improve cyber security and resilience in the UK.
The report collated the feedback from the APPG’s initial call for input and made clear some clear asks – notably the need for the Bill to widen its scope. As the first Act of Parliament to include “cyber” in the title, representing a fundamental step forward in how the UK approaches digital security. However, there is concern that this historic opportunity is too narrowly focused on compliance and prevention and not sufficiently ambitious in tackling some of the wider challenges that the UK faces.
This bill is a historic opportunity to strengthen the UK’s cyber resilience, but we risk falling short if we don’t listen to those on the frontline.
“We’re calling on DSIT to open up the conversation, coordinate across government, to provide a timeline and process for tackling the urgent issues that are deemed out of scope. By future-proofing regulations and giving parliament a clear role in oversight, we can make sure the UK remains secure and competitive in a rapidly changing digital world.”
Dan Aldridge MP, Chair of the APPG for Cyber Innovation
Enhancing communication between security and business leaders

Author: Marco Bresciani, Cyber Risk Enthusiast – CBN Board Member
Security leaders experience a continual trade-off between what they want to achieve and the resources that the organisation is willing to give them, be it funding, tools, suppliers, or people. At the same time, their executives need to quantify the financial loss that the organisation will incur if that specific risk happens.
This is not trivial: Gartner at the London 2024 event pointed out the need to “mind the gap” when reporting cybersecurity to management, providing different stakeholders with information they can act upon.
As someone who has worked in the cybersecurity industry since 1996, I have worked with banks and other regulated industries across EMEA, and realised many leaders avoid risk quantification due to misconceptions about data needs and complexity.
In this article I will highlight why cyber risk quantification (CRQ) serves as a vital purpose for security leaders, fostering better discussions with executives. Also, I will explain how organisations can achieve significant improvements in decision-making and risk prioritisation by debunking the myths on data complexity.
It’s not quantify vs qualify
CRQ has been the trusted method for actively communicating cyber exposure in an objective, well-grounded, and defensible manner for several years. It can be delivered in different ways. Most CRQ frameworks are based on the Value-at-Risk approach, developed in the Finance industry to measure the potential loss of investment portfolios.
A popular choice is the Open FAIR framework, an international, non-proprietary standard whose open nature and wealth of supporting documents helped increase its adoption by practitioners and consultants.
It’s important to remark that CRQ is not a replacement for a company’s risk management framework. The identification, analysis, evaluation, and treatment of risks are conducted as usual.
CRQ complements the qualitative output of common frameworks like COBIT or risk controls like ISO27000, by providing the “so what”, a means to compare losses deriving from risk scenarios, and the costs/benefits of mitigating actions.
The lessons learned from early adopters
Many organisations have tested CRQ in the past 5-8 years, often obtaining mixed results that made them question if introducing it in their risk management process was worth the effort. However, executives agree that when done right CRQ can foster confidence in security programs, by enabling informed decisions on cyber risk investments.
The initial stage of CRQ adoption highlighted some practical and some inherent problems:
- Too complex: CRQ may generate an analysis overload that doesn’t address business questions. It takes robust experience to avoid falling into a rabbit hole.
- Too manual: Stakeholders and subject matter experts are necessary to collect data and to interpret the results. Repeating the analysis implies re-engaging again with this cohort.
- Too static: Changes to risk exposure should be measured in near real-time, based upon live data. Integrating CRQ tools with monitoring feeds and asset data can be a big task itself.
Operationalising CRQ, even with a rigorous, well-structured, well-documented framework like FAIR, can be a real challenge.
How could we keep a CRQ initiative on the right path? The experience of early adopters suggest the following:
- Identify the use case that brings more value: for example, prioritising security initiatives and allocating budget, or choosing the correct cyber insurance coverage for your risk acceptance.
- Connect CRQ with business questions: does the extra effort solve a business problem? Else it’s just an intellectual pastime that doesn’t help risk owners in taking the right action.
- Use available data: inform risk scenarios with data from system telemetry and monitoring of third parties risk profiles.
- Automate CRQ where possible: to be a repeatable step that hits the window CRQ needs to be automated with a tool. The CRQ market, like the whole of cybersecurity, is experiencing disruption through automation and AI.
Conclusion
After the initial enthusiasm about a fresh new method and the sobering experience of delivering it, CRQ is maturing into a solid foundation to inform executive decisions about cyber risk.
More in general, CRQ is becoming an element of a broader data-driven approach to cyber risk management, where risk exposure is measured in quasi real-time, from within the organisation, across the third parties, and from the external threats.
Does it look too difficult? Remember that Lloyds made the first aviation insurance in 1911, when the “flying machine” industry was just 8 years old. Not much historical data was available to inform the decision, and possibly not many success stories too… Where there’s a will, there’s a way!
Enhancing supply chain cybersecurity resilience through positive storytelling and clear communication

Author: Liva Emmatty, Communications Lead at CBN
Recent disruptions caused by global IT outages have shed light on how a lack of IT supply chain diversification fundamentally undermines resilience by concentrating risk. Over the last few months, many organisations have been considering the makeup of their supply chains, and the strength of their incident management and response plans, accordingly.
As one of Clarity’s cybersecurity communications leaders, I work frequently with thought leaders and media navigating this environment in real time. As the communications lead for the Cybersecurity Business Network (CBN), a free community founded and managed by Clarity to provide a collective voice for UK’s cybersecurity companies, I have an additional, unique opportunity to consistently interact with cybersecurity experts. In the last month, I have also spoken with several cybersecurity leaders and teams at the International Cyber Expo, and during CBN’s webinar on how companies can bolster IT supply chains.
In this article, I will outline the communication challenges faced by cybersecurity leaders and organizations in this context, and the value powerful storytelling and clear communications can bring to cyber firms looking to boost reputations when trust is low.
To find out more information about Clarity and the ways in which we serve as a voice for UK cybersecurity companies, please visit Clarity’s website here: https://clarity.global/
Tackling supply chain obstacles that hinder business resilience
Many larger organizations have invested significantly in their cybersecurity practices, so some cybercriminals are focusing on weaker targets and entry points, like smaller businesses across the supply chain. Smaller organizations often don’t have the security and compliance expertise that larger companies do, alongside often having tighter budgets to fortify their systems.
The cybersecurity communications landscape doesn’t currently set these organizations up for success. A fear based narrative puts many off investing in the key technology they need to protect themselves, and means many put off building an ability to quickly respond to cyber-threats.
Cybersecurity communications challenges
Based on my recent conversations with the cybersecurity community, the key communications challenges the sector is currently battling are:
- A negative narrative – The overall cybersecurity narrative has often revolved around negative messaging, creating an environment of fear, anxiety, and stress. This can make many people shut down completely, meaning they don’t recognize the importance of addressing their cyber vulnerabilities effectively. While traditionally negative stories were focussed on cyberattacks, today this narrative also covers cyber firms ‘letting businesses and people down’ which has shaken brand trust and loyalty.
- Lack of awareness – Many smaller organizations underestimate the risk of becoming a target, and may not take cybersecurity seriously until they have been compromised. They need to understand that investing in cybersecurity is essential to safeguarding their operations, reputation, and sensitive data.
- Lack of understanding – The technical and specialized language used in cybersecurity can feel like jargon to those outside the sector, creating significant barriers to entry for many professionals. This might make them feel alienated or overwhelmed, meaning they automatically switch off unless there’s a simpler explanation.
How clear, positive communications helps businesses navigate the supply chain cybersecurity storm
Positive and clear communications build trust, support organizations to better anticipate potential cyberattacks, and foster a collaborative environment within the organization and in wider society. Key actions to take include:
- Positive and simple narratives: We need to change the messaging around cybersecurity, because the current approach is not working. Instead of tapping into fear and anxiety, companies need to highlight benefits of good cybersecurity practice like improved cyber resilience, better customer experience and building a trustworthy environment. This way we can transform a daunting necessity into an enabler of success, growth and opportunity.
- Educational campaigns: Sharing educational content pieces on social media platforms, brand websites, and webinars that highlight the gaps in the supply chain cybersecurity, and ways for the entire community to mitigate risks, will drive positive awareness. Storytelling and practical insights can be crucial to empower smaller businesses to adopt robust practices.
- Have a say in policy discussions: The recent global outage led to debates about the resilience of the UK’s networks, and the government proposed the new Cyber Security and Resilience Bill which will be introduced to ensure the security of critical infrastructure and digital services. While the sector will be watching closely for direction on how society will be better protected, the cybersecurity community has a responsibility to participate in the discussion and ask questions. For example, cybersecurity firms can delve into the concentration of risk: 62% of the global external attack surface is covered by just 15 companies. What is the long-term viability of reliance on so few suppliers?
- Transparency and visibility: Timely, accurate and clear communications increase transparency across the supply chain, ensuring all stakeholders are well informed and understand the current state and potential risks. This facilitates better decision making, fosters trust, and ensures a better management of issues before they escalate into a full-blown crisis. Open communication also enables companies to better align their objectives with suppliers and customers, supporting a resilient supply chain.
- Crisis management and recovery: During disruptions, effective communication channels are essential for coordinating crisis management efforts and recovery plans. This can help mitigate the crisis’ impact by ensuring swift decision making and resource allocation. Having clear and consistent messaging is imperative to maintain employee morale, maintain trust publicly, and ensure everyone has access to real-time updates and guidance to navigate the crisis.
Planning for 2025
As we approach year end, it’s time to reflect on key learnings and plan ahead. Have you thought about prioritising communications between your internal and external stakeholders? What are the key communication challenges you’re facing, and what support do you need to reach your objectives? Are you willing to lead the positive cybersecurity communications drive?
At Clarity, we specialize in supporting cybersecurity organizations to reach, inform, and educate their audiences using intelligence-led, measurable marketing and communications.
Want to find out more about how Clarity can support your cybersecurity business to grow and reach audiences with meaningful communications and smart marketing? Contact us here.For those interested in becoming a member of the CBN for free, or learning more about how you can contribute to and benefit from this initiative, please visit https://cb-network.org/
Key insights from the Supply Chain Resilience Webinar

The Cybersecurity Business Network (CBN) was delighted to host a webinar on supply chain resilience. Developed in response to the recent global IT outage, which exposed how reliance on only a few key suppliers can weaken critical systems, the webinar explored how businesses and policymakers can address the growing issue of how a lack of diversification in IT supply chains can increase the risk of major outages. The webinar brought together experts from cybersecurity, healthcare and academia to discuss ways to strengthen supply chain resilience and manage these risks. Below are some key takeaways from the event.
Dr. Melanie Garson, Cyber and Tech Geopolitics Lead at the Tony Blair Institute, opened the discussion by examining the global geopolitical landscape’s impact on supply chains. She emphasised the rising uncertainty and the interconnectedness of these risks, describing the current state as “a geopolitical state of upheaval.” According to Garson, the world’s IT supply chains are more vulnerable than ever due to increased global tensions and organisations must better anticipate the disruptions arising from cyberattacks and broader geopolitical events.
Simon Newman, Director of the Cyber Resilience Centre for London, reinforced this perspective by highlighting how attackers are now focusing on smaller, more vulnerable entities in supply chains. Newman also stressed the importance of enhanced collaboration across sectors, including law enforcement, to address these increasing vulnerabilities.
“As larger organisations have boosted their cybersecurity significantly, criminals are now targeting weaker entry points”, he explained, noting that smaller organisations often lack the resources to defend themselves effectively.
Simon Newman, Director of the Cyber Resilience Centre for London,
The healthcare sector’s supply chain vulnerabilities were a particular focus, with Rachel Dean, Head of Cybersecurity at NHS Supply Chain, providing insights. Dean emphasised that a successful cyberattack on the NHS’s supply chain could directly affect patient care.
“A successful cyberattack and the resulting inability to deliver operations impacts directly on the NHS’s ability to deliver patient care, which can have critical outcomes,” she warned.
Rachel Dean, Head of Cybersecurity at NHS Supply Chain
With a supply chain of over 6,000 suppliers, Dean explained the significant challenges in ensuring that each supplier meets necessary cybersecurity standards while avoiding creating barriers for smaller, critical suppliers.
On the regulatory side, Tim Rawlins, Director and Senior Advisor at NCC Group, discussed how regulations are evolving to address supply chain vulnerabilities.
“Regulators are increasingly focusing on requiring organisations to escrow software from their suppliers to reduce risk.”
Tim Rawlins, Director and Senior Advisor at NCC Group
While regulation is a key driver of improvement, Rawlins stressed that organisations themselves must take proactive steps to manage third-party risks and understand how disruptions in one part of the supply chain can have wide-reaching consequences.

Digital Dawn: Cyber Security Policy in the Wake of Political Change
An NCC Group cyber policy report providing a strategic guide for political and business decision makers worldwide.
Our report emphasizes just how important it is for
incoming governments to stay focused on cyber
security and resilience amidst the many competing
priorities they will face…. It’s clear that governments taking
appropriate action to keep their citizens safe will be
critical to maintaining trust in public institutions and
unleashing the huge potential of the digital economy.Mike Maddison
CEO at NCC Group
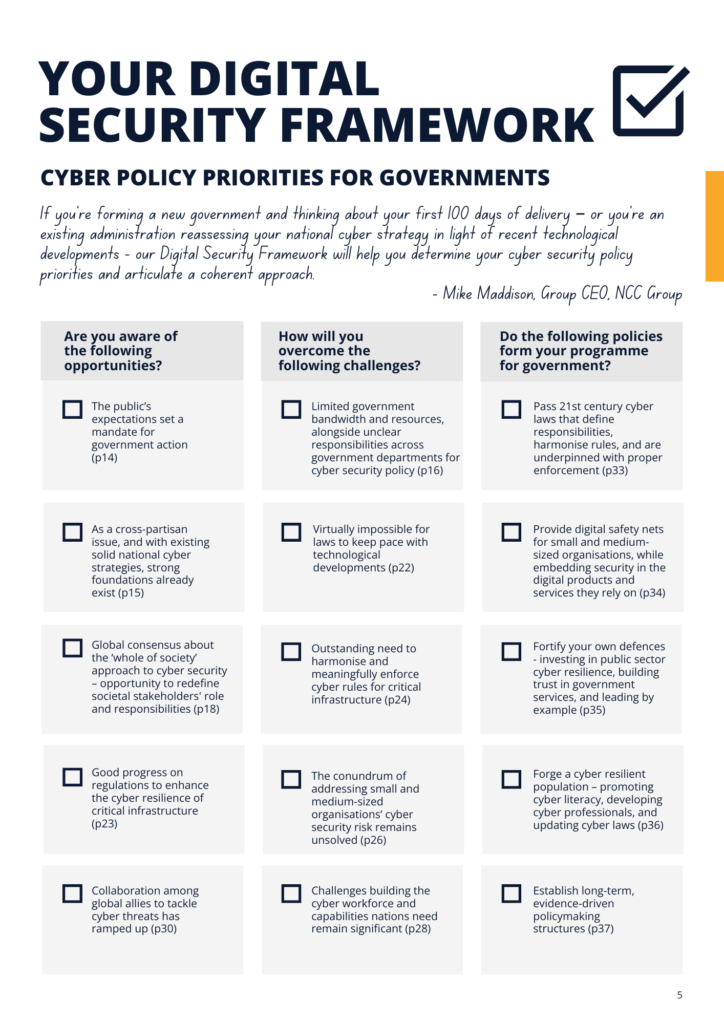
In this bumper election year, the report offers new and existing governments a deeper understanding of how their counterparts in other areas of the world are tackling similar cyber security issues.
The findings explore:
- The role of government in securing cyberspace
- The cyber security opportunities and challenges governments face in 2024
- NCC Group’s recommendations for the top five cyber priorities for governments
Drawing from NCC Group’s insights and new research, which included commissioning polling from J.L. Partners to examine public opinion on cyber security issues and conducting interviews with key people from across the global cyber policy ecosystem, the report urges policymakers to establish long-term digital resilience.
NCC Group identifies five key policy areas it believes new and existing governments must prioritize to achieve this in practice:
1. 21st-century cyber laws that define responsibilities, harmonise rules, and are underpinned with proper enforcement.
2. Digital safety nets for small and medium-sized businesses and organisations, embedding security in the digital products and services they rely on.
3. Fortifying government defences by investing in public sector cyber resilience, building trust in government services, and leading by example.
4. Forging a cyber resilient population – promoting cyber literacy, developing cyber professionals, and updating cyber laws.
5. Long-term, evidence-driven policymaking structures.
We are proud of NCC Group’s latest contribution to the cyber policy debate. Cyber security is a matter of national and global importance and we are passionate about ensuring that cross-party consensus does not lead to complacency in this bumper election year and beyond. We look forward to working with incoming governments in the UK, and worldwide, to implement ambitious but actionable policies that will take national, organisational and individual cyber security to the next level.
Kat Sommer
Group Head of Government Affairs & Analysts Relations, NCC Group
CBN Advisory Board
Some of our key takeaways from the report include
- Policy decision makers should prioritise cybersecurity policy, even if it isn’t a vote winner, as it’s a key enabler of resilience and economic growth.
- Cybersecurity policy making should be less siloed and greater dialogue across Government should be encouraged.
- Security needs to be built into supply chains to ensure organisations of all sizes and structures have built in resilience.
- Public private partnerships and discourse is paramount to build a future that is secure against malicious actors and nation states.
